Discovery
Security Starts With Knowing Your Clouds
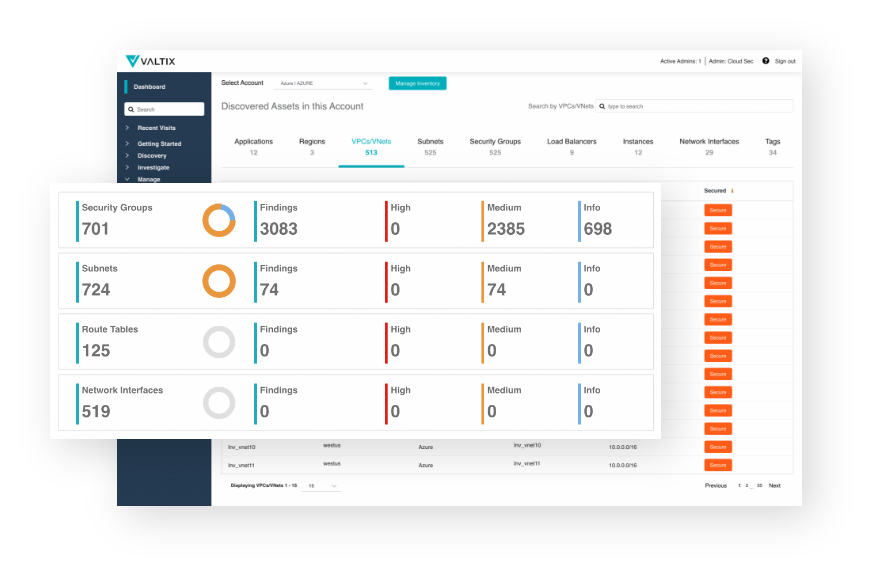
Valtix delivers visibility through the discovery of cloud apps, cloud networks, and other infrastructure. We help organizations like yours with continuous discovery to ultimately enable complete and confident deployment of network security controls to achieve cloud security objectives and satisfy compliance requirements.
Continuous
Visibility
Real-time visibility into applications, cloud networks (VPC/VNET), network traffic logs, indicators of compromise, and geo-location among others
Connect
Discovery to Defense
One-click deployment of security controls and automation through tag-based policy makes securing new apps or infrastructure simple and more effective
How Many Apps Do You Have Across Every Cloud, Right Now?
Unless you can answer this question, you can’t secure your cloud infrastructure. Many tools scan to collect insights to inform cloud security posture decisions. Only Valtix connects discovery to defense, surfacing gaps in coverage, and then simplifying identification of best practices and deployment of security controls.

“Using Valtix we get continuous visibility of egress traffic to prevent exfiltration and add velocity to our security operations through Terraform and simplicity of a SaaS model.”
Albert Chow IT Director
Continuous Insight With No Agents or Scans
Real-Time Inventory of Assets
Current and complete visibility into every cloud region, application, load balancer, VPC/VNet, security group, and more. Integrated map view provides geographic insight on the location of every asset and threat.
Platform-as-a-Service (PaaS) Visibility
Gain visibility into 100s of PaaS services such as AWS S3, Azure SQL, or Google Cloud GKE. Identify which services are being utilized within your accounts and applications. Determine if malware might be stored and which instances might be connecting to it.
Cloud DNS & VPC Flow Telemetry
Unlock critical visibility into security telemetries such as DNS logs for intent and VPC flow logs for actual behavior with integrated threat intelligence to drive detection & investigation of potential threats.
Network Security Deployment Insight
Gain insight on network security gaps with built-in recommendations on how to remediate them.
Is Your Cloud Infrastructure Secure?
Learn Best Practices in Cloud Network Security