Valtix Introduces Support for AWS Gateway Load Balancer and URL Filtering Categories (powered by BrightCloud)
A persistent need in securing outbound traffic to the Internet is to ensure that connections only go to trusted locations. This prevents exfiltration, blocks command-and-control (C2) traffic and stops hijacked instances from connecting into malware botnets. Use of URL and domain categories (finance, healthcare, adult, gaming etc) allows cloud administrators to quickly create organization-wide and app-specific policies. This protects workloads that need regulatory compliance such as PCI, HIPAA and SOX which need to protect sensitive data from connecting to unauthorized destinations.
Support for AWS Gateway Load Balancer (GWLB) simplifies adding network security for securing egress and east-west traffic (between VPCs). Using GWLB a single set of auto scaling Valtix Gateways can inspect all traffic from multiple spoke VPCs connected to an AWS Transit Gateway. Customers can enable GWLB with one-click in the supported AWS regions.
The addition of TLS decryption exceptions, for individual domains or categories, in this release provides a complete feature set for building a secure outbound access policy for enterprise workloads running in public clouds. As a service, Valtix makes this easy to achieve, in minutes, without requiring deep expertise in security or complex automation and licensing. As a usage-based service Valtix provides all its features for a single hourly price.
New Features in Release 2.5
Here’s a quick summary of the features in this release:
- AWS Gateway Load Balancer (GWLB) – a simple native AWS solution to deploy and manage network security services in a horizontally scalable and fault-tolerant manner.
- URL and Domain (FQDN) Filtering Categories (powered by BrightCloud) – prevent exfiltration by stopping connections to command-and-control (C2) while allowing outbound traffic only to approved destinations.
- TLS Decryption Exceptions – ensure that TLS decryption is not applied to trusted sensitive sites like financial services or healthcare to ensure privacy and compliance.
- Network Security Insights **(*****preview)*** – Find insights into your cloud deployment’s network security configuration, which instances have open outbound security groups, or which instances have public IP’s attached to them.
- Antivirus/Malware inspection – inspect traffic flows for viruses and malware with an AV engine.
- Bring Network Security Alerts into your Slack Channels – the title’s self explanatory; takes 1 minute to setup.
To learn more about the previous release (version 2.4) see here.
Upgrade Steps
As a reminder – In true cloud-native style the Valtix Controller (aka management plane) has all the latest features upgraded automatically; existing features and settings continue to work normally. And, the Valtix Gateways (aka dataplane) that are running in customer cloud accounts can be upgraded with a one-click blue/green hitless upgrade, i.e. fully under customer control. To learn more about upgrade steps, see documentation (inside your Valtix portal) and how do I use/deploy these features?
AWS Gateway Load Balancer (GWLB)
AWS Gateway Load Balancer brings a cloud-native approach for inspecting network traffic with advanced network security services. Customers can simply select the VPCs that need to be protected, and enable AWS Gateway Load Balancer in Valtix Controller. That is all the customer needs to enable, Valtix cloud security service does the rest behind the scenes: receives the traffic from the VPC via Transit Gateway connected VPCs or a Gateway Load Balancer Endpoint (GWLBE) in the VPC, inspects the traffic based on customer-configured policies, and then allows or blocks the traffic. This provides a network security capability similar to how AWS provides load balancing as a service with the Application Load Balancing (ALB). Gateway Load Balancer simplifies network security architecture by providing a single entry point for all deep packet inspection requirements, and together with Valtix it enables a service-oriented approach for security. At launch, AWS plans to support GWLB in us-east-1 (N. Virginia), us-west-2 (Oregon), eu-west-1 (Ireland), ap-southeast-2 (Sydney), and sa-east-1 (Sao Paulo).
See here to learn more about the integration of Valtix with AWS Gateway Load Balancer.
Why is URL and Domain Filtering Important for Outbound/Egress Flows?
Outbound traffic presents the biggest threat for enterprise deployments in public clouds because any public cloud asset is just “one step” away from the Internet. And there are no effective controls to inspect or stop any malicious activity (details below). That means attackers in your cloud network or malicious insiders can easily exfiltrate confidential information to their command-and-control networks, or convert enterprise workloads into a malware botnet launching attacks. This can be seen in the BrightCloud Threat Report 2020 which shows the top URL/domain categories hosting malware. So it’s important to inspect the outbound flows of your cloud workloads with URL/domain filtering and relevant antivirus inspection engines. 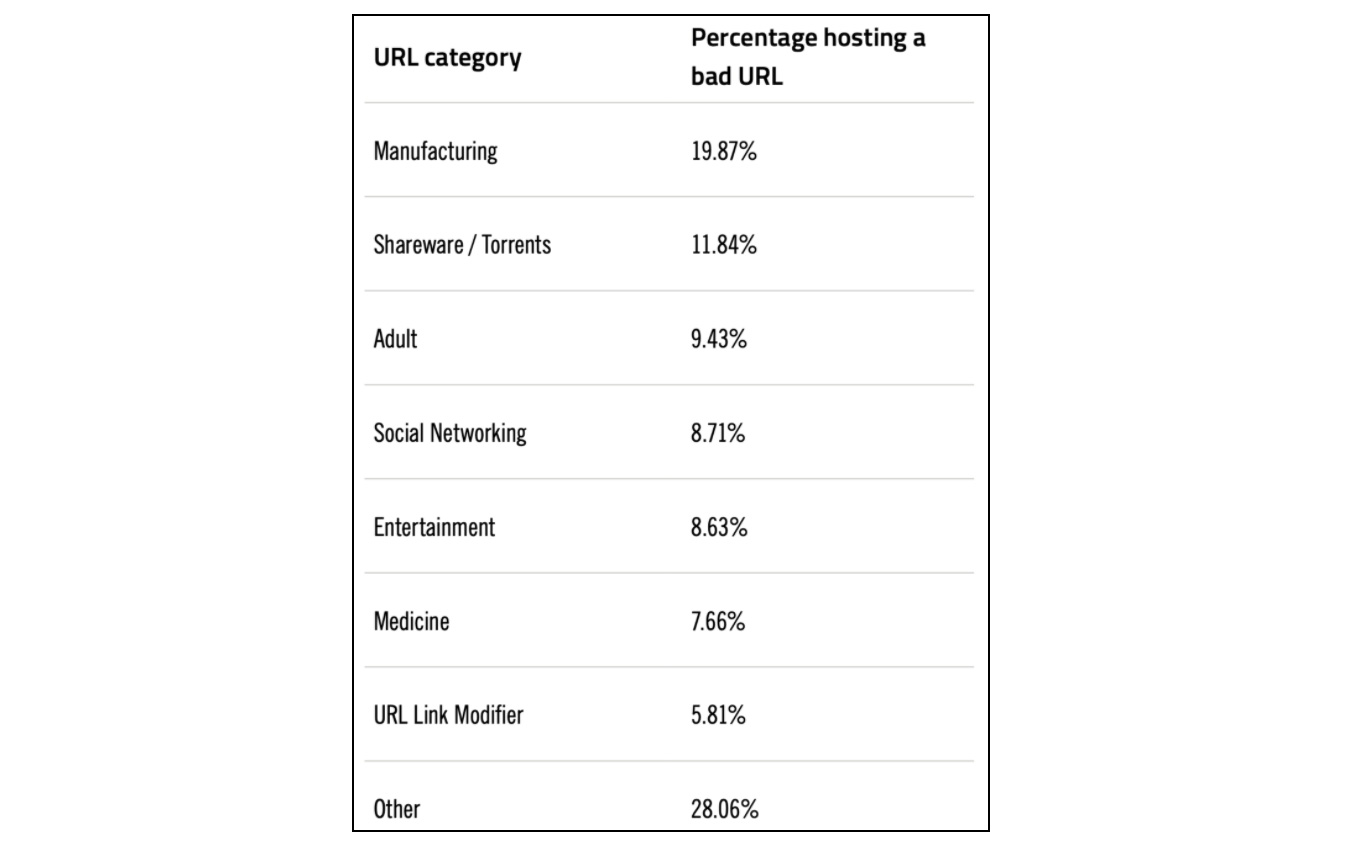
BrightCloud Threat Report 2020: Top site categories hosting malicious URLs in 2019
So what are the default controls? In most public clouds the only outbound controls are the security groups where customers can configure either:
- Allow all outbound traffic (0.0.0.0/0) on all ports from all instances and PaaS inside your cloud deployment. This is the default configuration in all public clouds.
- Or add specific IP addresses that you want to block/deny or allow, on specific ports. This is practically unusable in terms of normal usage as its not possible to list all good sites (who’s IP addresses can change frequently), or bad sites (who are notorious in changing their source identifiers).
URL and Domain Filtering Categories – powered by Bright Cloud
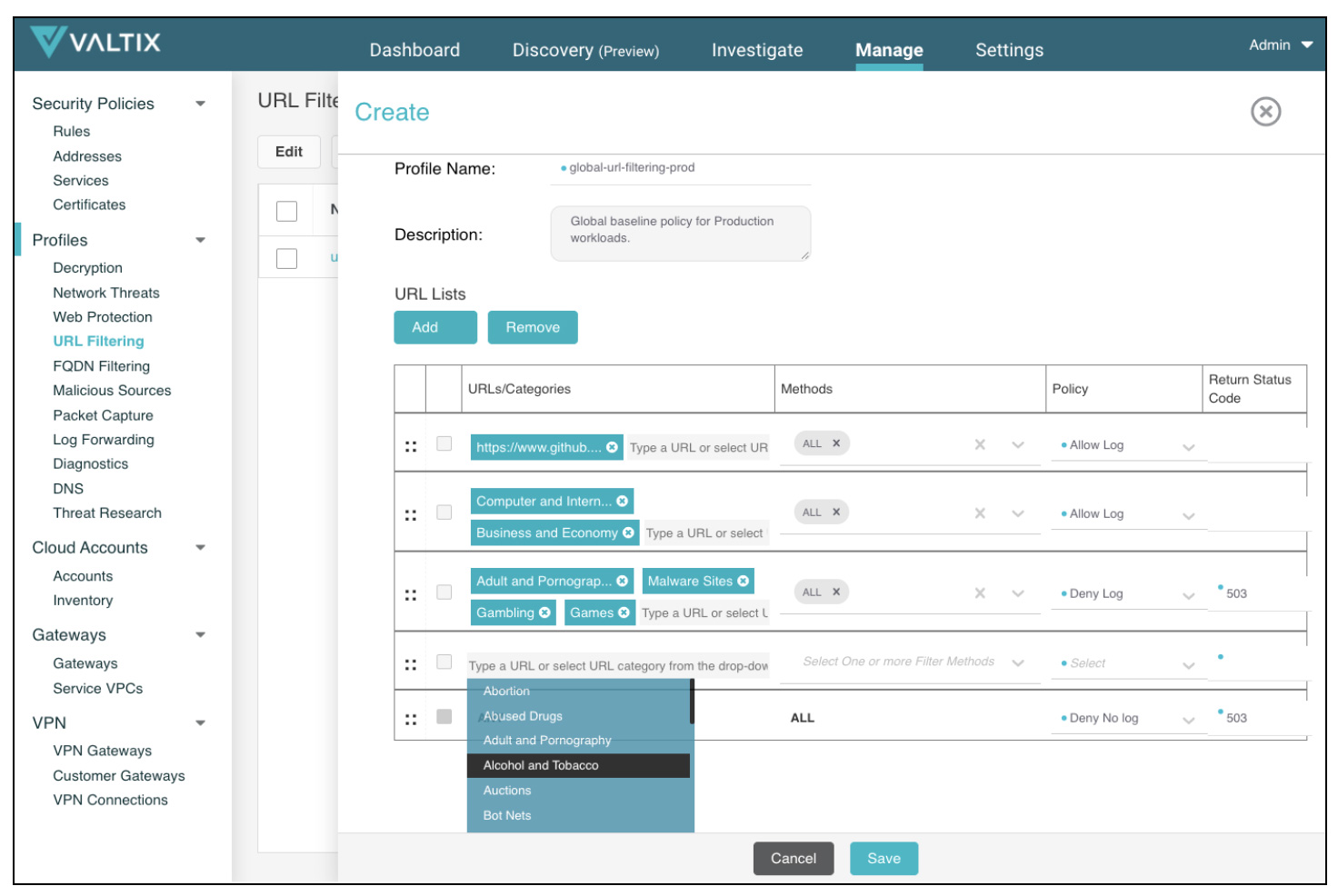
Prior to this release, Valtix supported egress filtering with custom lists of URLs and fully-qualified domain names (FQDN). This allowed customers to control traffic to specific egress destinations. This release adds support for URL and domain categories powered by BrightCloud Threat Intelligence which uses 95+ Million sensors providing category classification. That means that you can create general purpose policies that allow specific approved categories while blocking command-and-control and malware sites.
Support of domain and URL filtering categories from BrightCloud provides coverage across:
- 84 categories (financial services, healthcare, government, adult, gaming, malware etc) for URL with domain and path-specific information
- 842+ Million domains
- 37+ Billion URLs
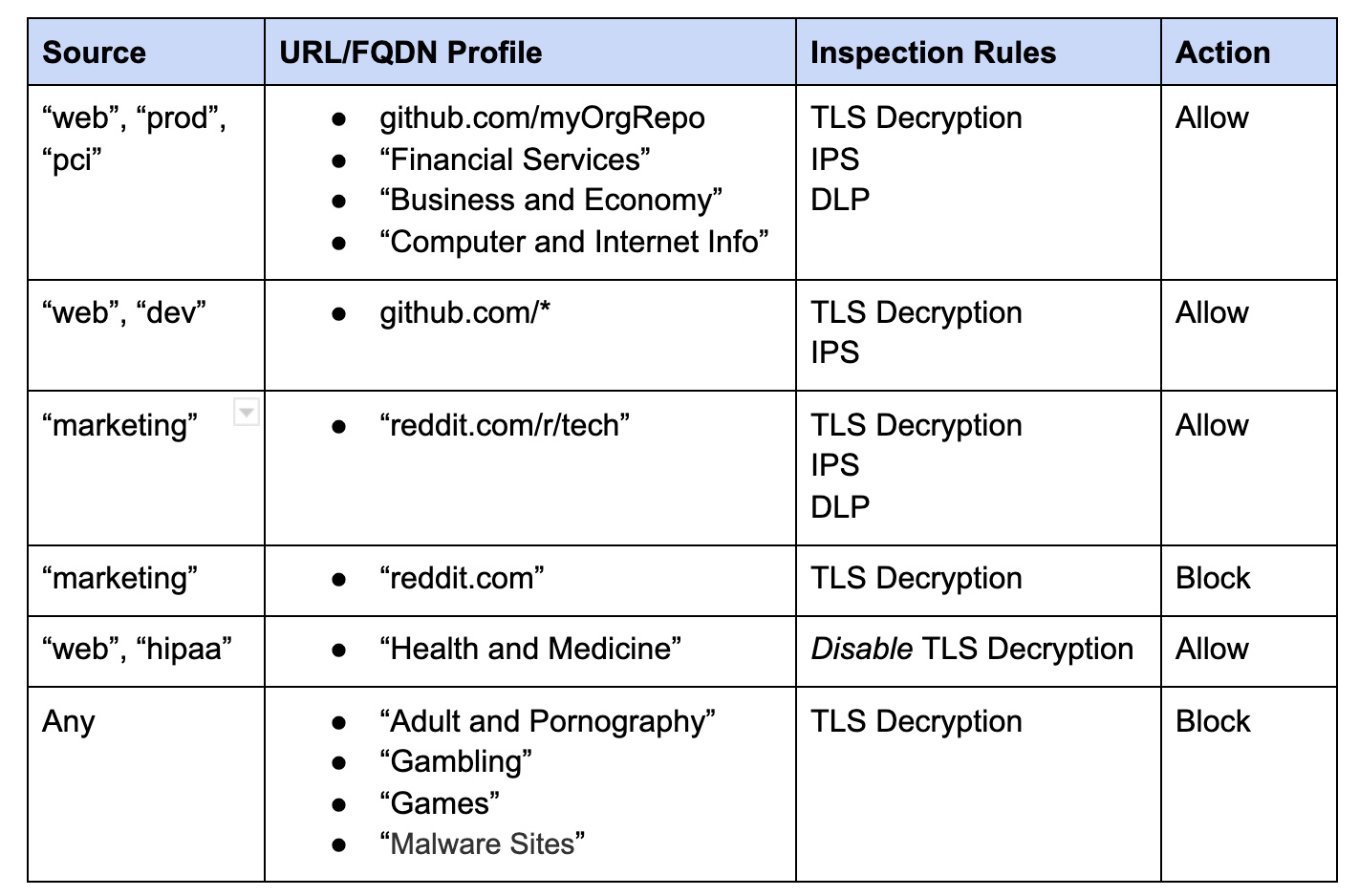
Valtix security policies for egress can now leverage the tags on your cloud assets discovered when onboarding your cloud accounts (i.e. meta-data such as security groups, VPC ID, user-assigned tags like “web”, “dev”, “prod”, “pci” etc) to write intelligent rules that provide attributed-based asset control (ABAC).
Here are some example Valtix policies that combine tag-based policies, including protections for data loss prevention (DLP) to ensure sensitive data is not stolen from production workloads:
Disable TLS Decryption
Usually, enabling TLS decryption is a best practice since this allows the Valtix Gateways to inspect traffic (in forward proxy or reverse proxy mode). In case of outbound flows, this is required to determine the exact URL being accessed. But in some cases, due to privacy or regulatory compliance reasons, it may be required to not decrypt traffic to certain domains/FQDNs, either for specific sites or entire domain categories.
Valtix now supports both of these options as shown in the example above where traffic from “hipaa” tagged instances sent to “Health and Medicine” sites is not decrypted since it may contain sensitive medical information.
Network Security Insights (Preview)
The Security Insights feature builds on the Discovery features of Valtix to provide information on the network security misconfigurations in a customer’s cloud environment. This combines configuration information with exposed assets such as instances to provide a clear dashboard with severity levels. This is driven by pre-built and customer-configured rules. Users can create queries based on discovered information and generate rules, including setting severity levels.
For example: how many instances have outbound security groups that are wide open (0.0.0.0/0), or which instances have public IPs assigned to them, or security groups with inbound ports that are wide open and instances that are exposed, or for specific sensitive ones such as 22 (SSH). Security Insights covers several cloud assets including security groups, ports, VPCs, network interfaces, load balancers (and their certificate status) and route tables. Over subsequent releases this feature will be expanded to offer more insights that help security teams continuously secure their cloud environments.
Antivirus/Malware Inspection
Antivirus/Malware inspection is essential to ensuring that files being passed in traffic does not contain viruses. This ensures that your cloud workloads are not being used for malware distribution as part of botnet, and also attackers are not easily able to download known malware/viruses into your environment if they evade other defenses. Future blog posts will cover how this is an important part of a multi-layer defense strategy. AV inspection is a profile you can add to an existing security rule with a few clicks.
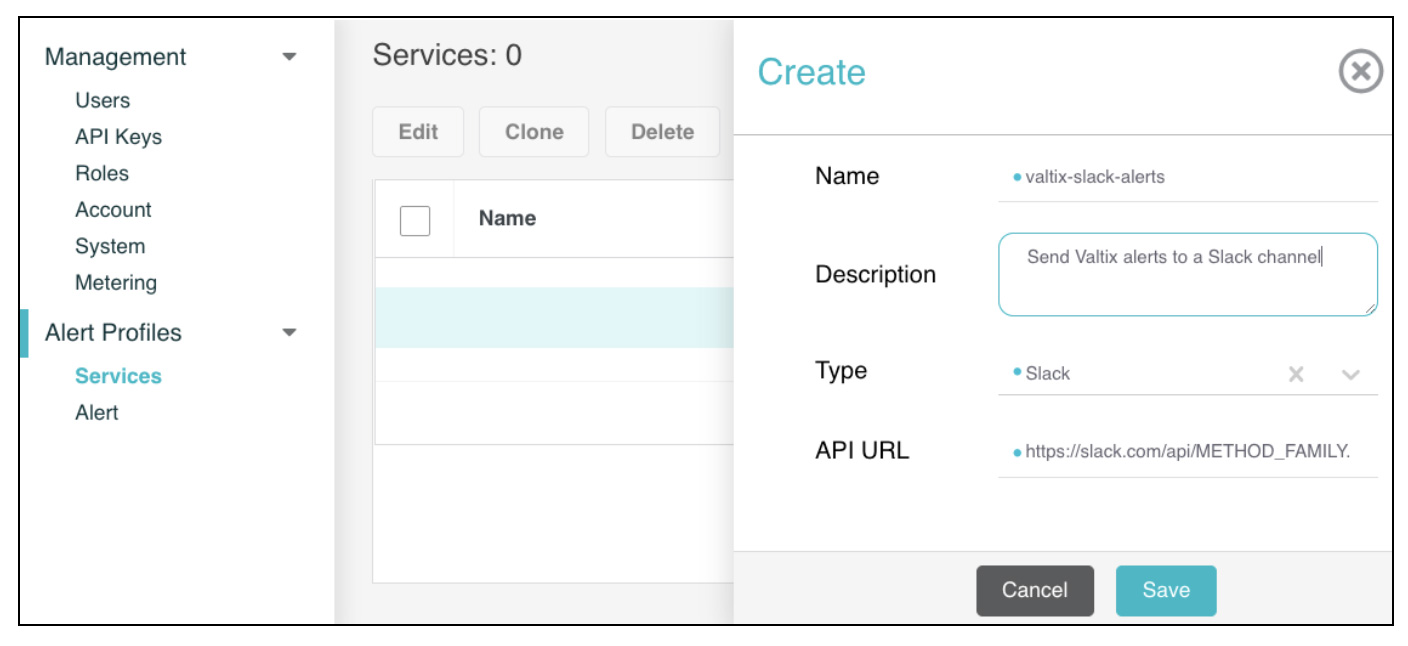
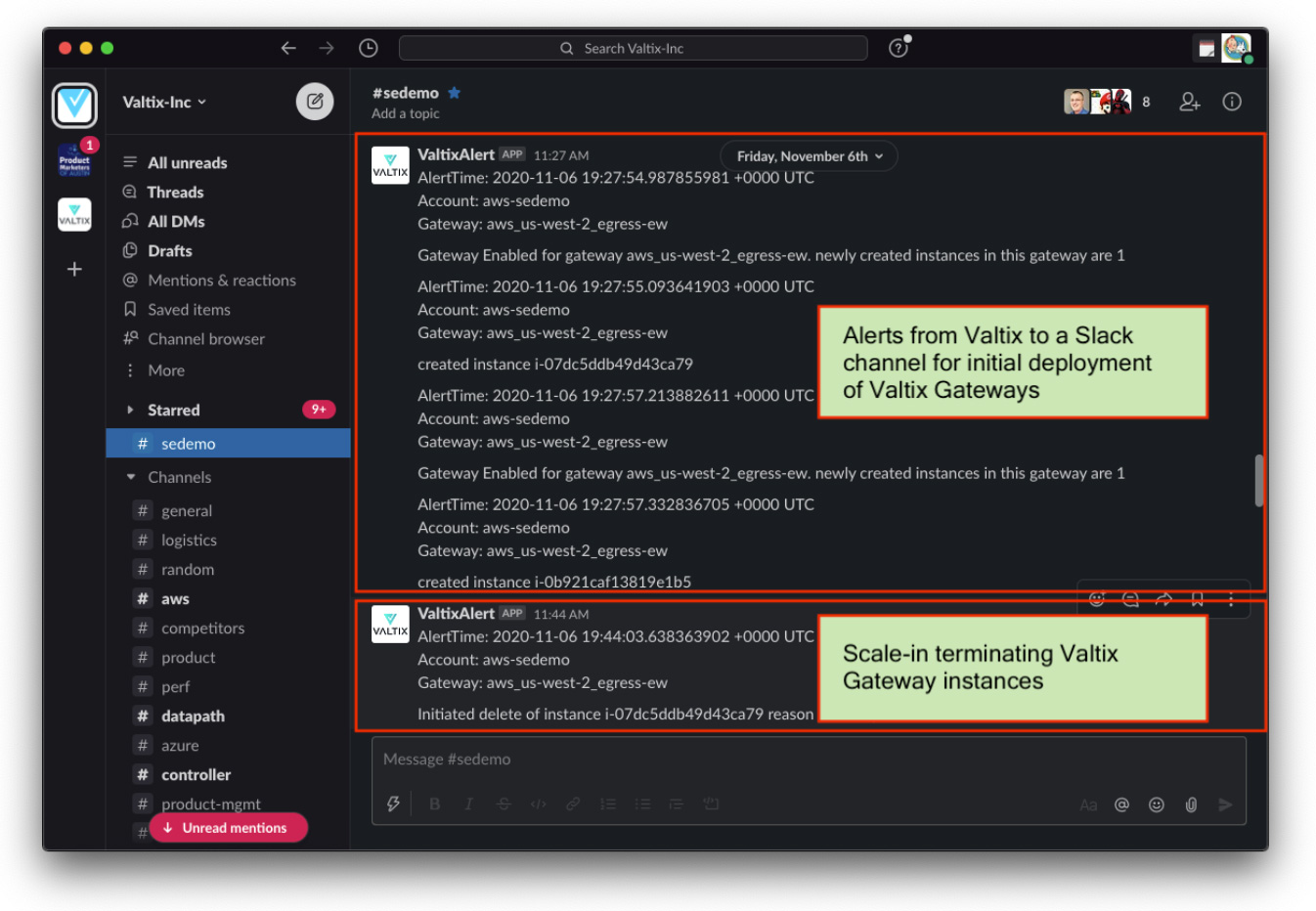
Bring Network Security Alerts into your Slack Channels
It goes without saying that Slack has become integral to how teams work together, especially in current times. Slack has also become a useful place for operations teams to receive relevant messages and act with human or automated actions. Valtix has now added Slack integration to allow alerts to be sent to a Slack channel. In addition to Slack, Valtix also supports forwarding alerts to PagerDuty and ServiceNow.
And it only takes a few minutes to set this up:
- Go to your Slack to setup your incoming webhook calls: https://api.slack.com/messaging/webhooks
- From Valtix SaaS portal > Settings > Alert Profiles > Services: Add details of your Slack environment including the webhook API for the relevant Slack channel.
- From the Alert Services > Alerts setup the forwarding rules to get the relevant alerts for System-level, Gateway or Discovery (Security Insights).